For those who haven’t heard:
Decoding the Chinese Super Micro super spy-chip super-scandal: What do we know – and who is telling the truth? • The Register
Who is telling the truth and why?
Please absolutely avoid political commentary and stick to the technical plausibility and practical issues between the statements released by all parties involved.
Decoding the Chinese Super Micro super spy-chip super-scandal: What do we know – and who is telling the truth? • The Register
Who is telling the truth and why?
Please absolutely avoid political commentary and stick to the technical plausibility and practical issues between the statements released by all parties involved.
My understanding is that because it’s operating near the processor it can execute commands in a manner somewhat impervious to higher level software layers.
The likelihood seems to me low that all involved companies would all outright deny in a blanket manner such a vulnerability when any lack of transparency in the matter could mean unprecedented decimation of stockholder trust and opening themselves up to a legal hellfire raining down upon them.
Of course not that the technology does not exist or this has been seen before, but I’m questioning the scale, the (successful) targets, etc.
I’m wondering the complexity of design, fabrication and implementation of a chip that size and bypassing detection of 2 of the largest technology companies on the planet.
And if those involved in the hardware industry have seen this before and what were the particulars.
I believe Super Micro provides server hardware to the military / NSA etc. as well?
What are the mil spec guidelines for accepting foreign made server hardware? I doubt they sustain themselves on, or that it’s even possible to source, computing power made on US soil.
The likelihood seems to me low that all involved companies would all outright deny in a blanket manner such a vulnerability when any lack of transparency in the matter could mean unprecedented decimation of stockholder trust and opening themselves up to a legal hellfire raining down upon them.
Of course not that the technology does not exist or this has been seen before, but I’m questioning the scale, the (successful) targets, etc.
I’m wondering the complexity of design, fabrication and implementation of a chip that size and bypassing detection of 2 of the largest technology companies on the planet.
And if those involved in the hardware industry have seen this before and what were the particulars.
I believe Super Micro provides server hardware to the military / NSA etc. as well?
What are the mil spec guidelines for accepting foreign made server hardware? I doubt they sustain themselves on, or that it’s even possible to source, computing power made on US soil.
I believe Super Micro provides server hardware to the military / NSA etc. as well?
What are the mil spec guidelines for accepting foreign made server hardware? I doubt they sustain themselves on, or that it’s even possible to source, computing power made on US soil.
I agree. Even big banks test hardware for malicious firmware, military definitely does, they are likely the primary target for this sort of hack. Its hard to believe this got past such big industry names, but I guess not impossible.
I find the story highly plausible. Putting backdoors in technology has gone on for decades. The more complex the technology, the harder it is to detect a backdoor. A good backdoor won't do much network traffic so it will be hard to spot.
I have always been surprised that companies and governments seem willing to buy important infrastructure equipment from potential adversaries.
I have always been surprised that companies and governments seem willing to buy important infrastructure equipment from potential adversaries.
here's a smarter approach: Photos of an NSA “upgrade” factory show Cisco router getting implant | Ars Technica
not a secret chip but a camera. The photo of a circuit board is wrong. There was no electronic circuitry in a 914. Only relays and switches.
Popular Science - Google Books
Popular Science - Google Books
I bet that popular science just used a modern photocopier innards as the circuit board for the art in the photo. Looks similar to a 68000 cpu based fax machine mobo to me.
What suprised me was that they only had access to Soviet secrets from 1962-1969. Then again as far as exploits go that is a pretty long run.
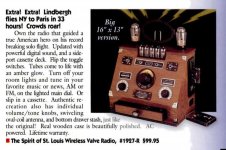
1997 popsci issue. ahh the part of the 90s when it was popular to have a tv tuner and radio inside of your computer (I'm referring to page 40), funny how today I use the computer to get away from the tv and radio and all the other drudgery known as mainstream media. Its almost like they didn't want us researching stuff online or on cdrom or playing video games or doing real work so they stuck a tv tuner inside of our computer to tempt us to go back to watching television. conspiracy much?
Or sell us useless stuff, its no wonder our world is so screwed if this is what we've been buying, its pure evil too because it looks so good, so tempting to buy one:
What suprised me was that they only had access to Soviet secrets from 1962-1969. Then again as far as exploits go that is a pretty long run.
1997 popsci issue. ahh the part of the 90s when it was popular to have a tv tuner and radio inside of your computer (I'm referring to page 40), funny how today I use the computer to get away from the tv and radio and all the other drudgery known as mainstream media. Its almost like they didn't want us researching stuff online or on cdrom or playing video games or doing real work so they stuck a tv tuner inside of our computer to tempt us to go back to watching television. conspiracy much?
Or sell us useless stuff, its no wonder our world is so screwed if this is what we've been buying, its pure evil too because it looks so good, so tempting to buy one:
Attachments
Last edited:
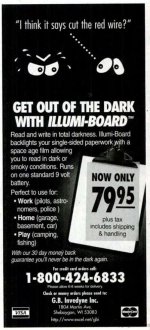
no way! a glow in the dark clipboard!
With a 'space age film' no less

I find the story highly plausible. Putting backdoors in technology has gone on for decades. .
It can be very useful.
For example if someone sold some software online then the payment was bounced the software could be disabled via the internet the next time it phoned home.
- Status
- This old topic is closed. If you want to reopen this topic, contact a moderator using the "Report Post" button.
- Home
- Member Areas
- The Lounge
- Chinese Spy Chips in Supermicro Boards